
July 14, 2025
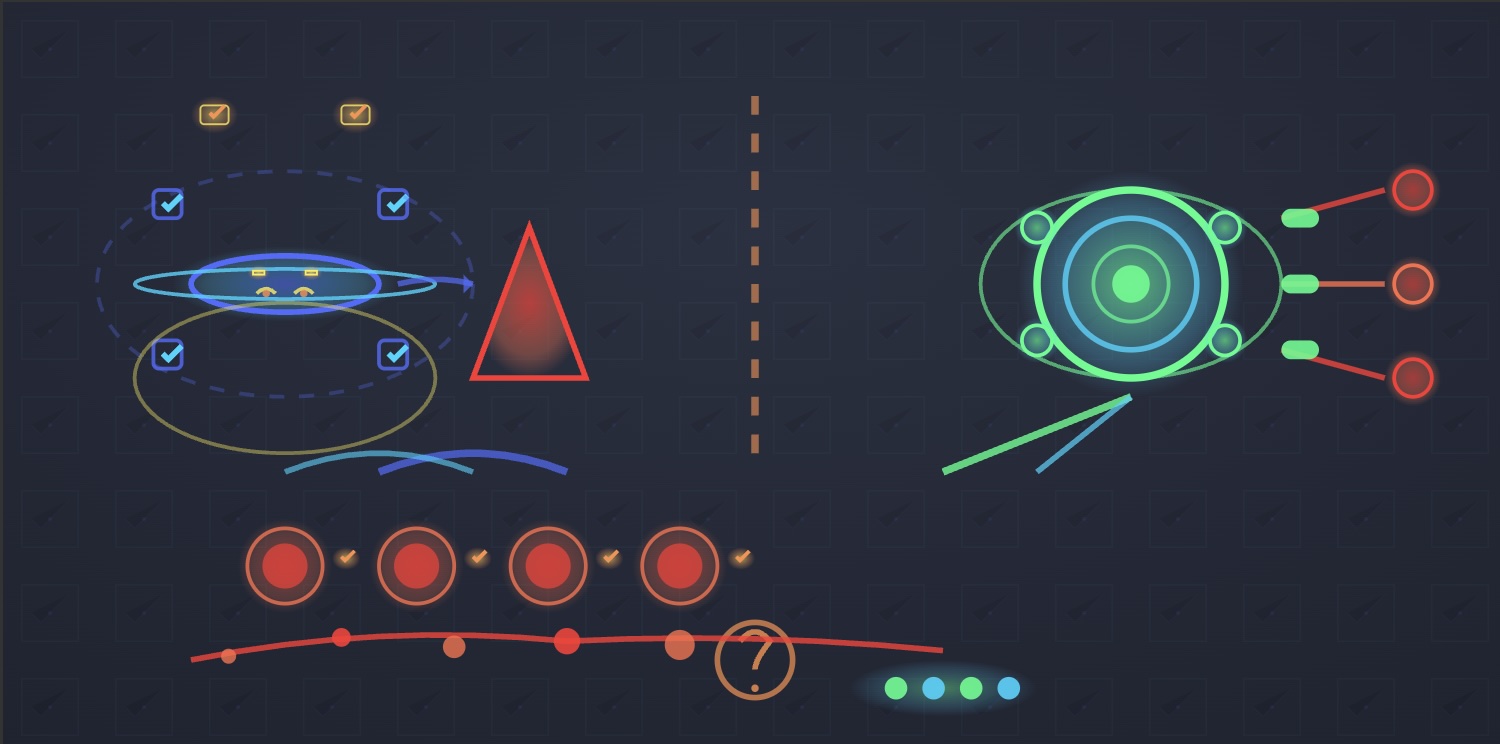
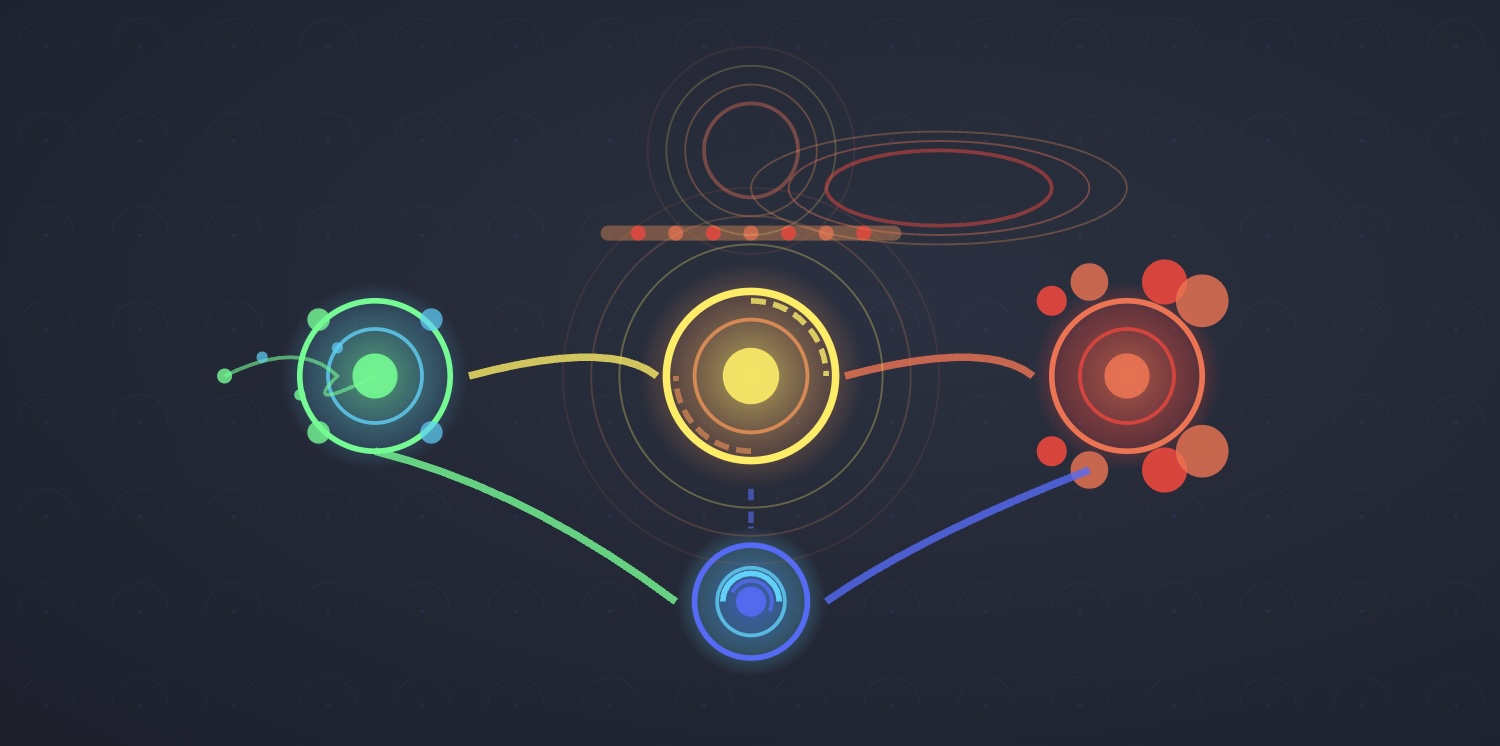
Collective Defense and Patch Management
Collective defense brings entities together against common threats. IT Agent extends this principle to patch management, providing crowdsourced deployment data that transforms cautious, fear-based patching into confident, data-driven vulnerability remediation.
Read More →

July 14, 2025
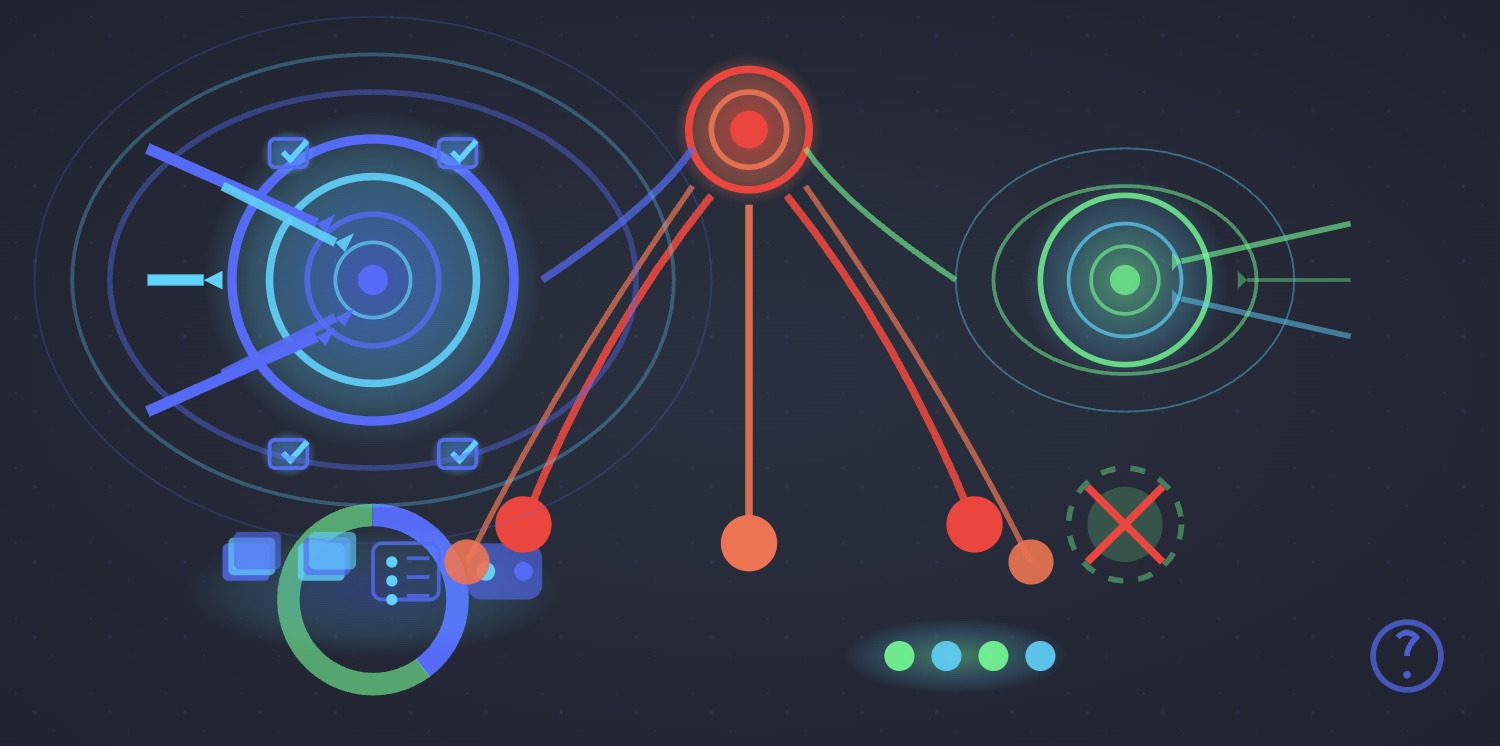
What is Vulnerability Prioritization?
Vulnerability prioritization determines which unpatched vulnerabilities pose the greatest cyber risk and should be addressed first. Modern platforms like IT Agent provide real-world patching data to optimize remediation strategies.
Read More →

July 14, 2025
Community Intelligence and Patch Management
IT Agent applies the principle of community intelligence to patch management: crowdsourcing data to identify the 2% of patches that cause disruption while confidently fast-tracking the 98% that deploy safely.
Read More →
July 14, 2025
True Differentiation in Cybersecurity
In a crowded cybersecurity market, true differentiation means solving problems no one else addresses. IT Agent's crowdsourced patch intelligence represents a fundamentally different approach to vulnerability remediation.
Read More →
July 14, 2025
Reston Cybersecurity Startup IT Agent Aims to Transform Software Updates
IT Agent, a Reston-based cybersecurity startup founded by former NSA engineer Mike Starr, emerged from stealth mode with $3.35 million in seed funding. The platform functions like "Google reviews for security patches."
Read More →
July 14, 2025
The Closer and the IT Pro
Baseball closers and IT professionals share a challenging reality: they can only lose, never truly win. Success goes unnoticed while failures become front-page news.
Read More →
July 14, 2025
If It Ain't Breaking Stuff, Fix It
With less than 2% of patches requiring rollback, the real solution isn't identifying problematic patches—it's providing data about the 98% that deploy safely, enabling aggressive patching.
Read More →
July 14, 2025
Server Patching: A Comprehensive Guide
Server patching updates software to fix security vulnerabilities and bugs, yet less than 2% of patches cause disruptions. Modern crowdsourced patch intelligence platforms provide deployment safety data.
Read More →
July 14, 2025
IT Agent vs. ChatGPT
We explored vulnerability remediation through the Russian Roulette metaphor, then challenged ChatGPT to do the same. Compare both perspectives on why organizations struggle with patching.
Read More →

July 14, 2025
Breaking the Cycle of Cybersecurity PTSD
The cybersecurity industry faces an unprecedented crisis: 46% of professionals report increased stress levels, with nearly half considering leaving the field entirely.
Read More →
July 14, 2025
Even ChatGPT "Thinks" Patching Vulnerabilities is the Best Way to Secure an Organization
Even AI agrees: regular vulnerability patching is the foundation of enterprise security. With less than 2% of patches requiring rollback, the real challenge is identifying potential issues.
Read More →
July 13, 2025
Consider the Human Factor in Cyber Breaches
While organizations obsess over phishing training, the real human factors in cyber breaches—misconfigured servers, unpatched vulnerabilities, and overworked IT teams—remain largely unaddressed.
Read More →

July 11, 2025
Zero Days: The Paradox of Urgency in Vulnerability Management
Zero-day vulnerabilities get aggressive patching treatment while older vulnerabilities languish for months—yet 75% of ransomware attacks exploit vulnerabilities from 2019 or earlier.
Read More →
July 11, 2025
Is the Cybersecurity Community's Obsession with Compliance Counter-Productive?
While organizations spend countless resources achieving compliance standards, major breaches continue affecting compliant companies—suggesting box-checking distracts from stopping attackers.
Read More →
July 11, 2025
The Cost of Compliance: What Charles Goodhart, Bill Murray, and Cybersecurity Have in Common
CISOs spend up to 40% of cybersecurity budgets on compliance reporting while cyberattacks continue rising—illustrating how compliance metrics obscure the real goal.
Read More →
July 11, 2025
Let's Ease Up on the Cyber Criminal High Tech Hype
While media focuses on exotic AI-powered attack methods, cybercriminals continue succeeding with the same basic techniques—unpatched vulnerabilities, stolen credentials, and phishing.
Read More →

July 11, 2025
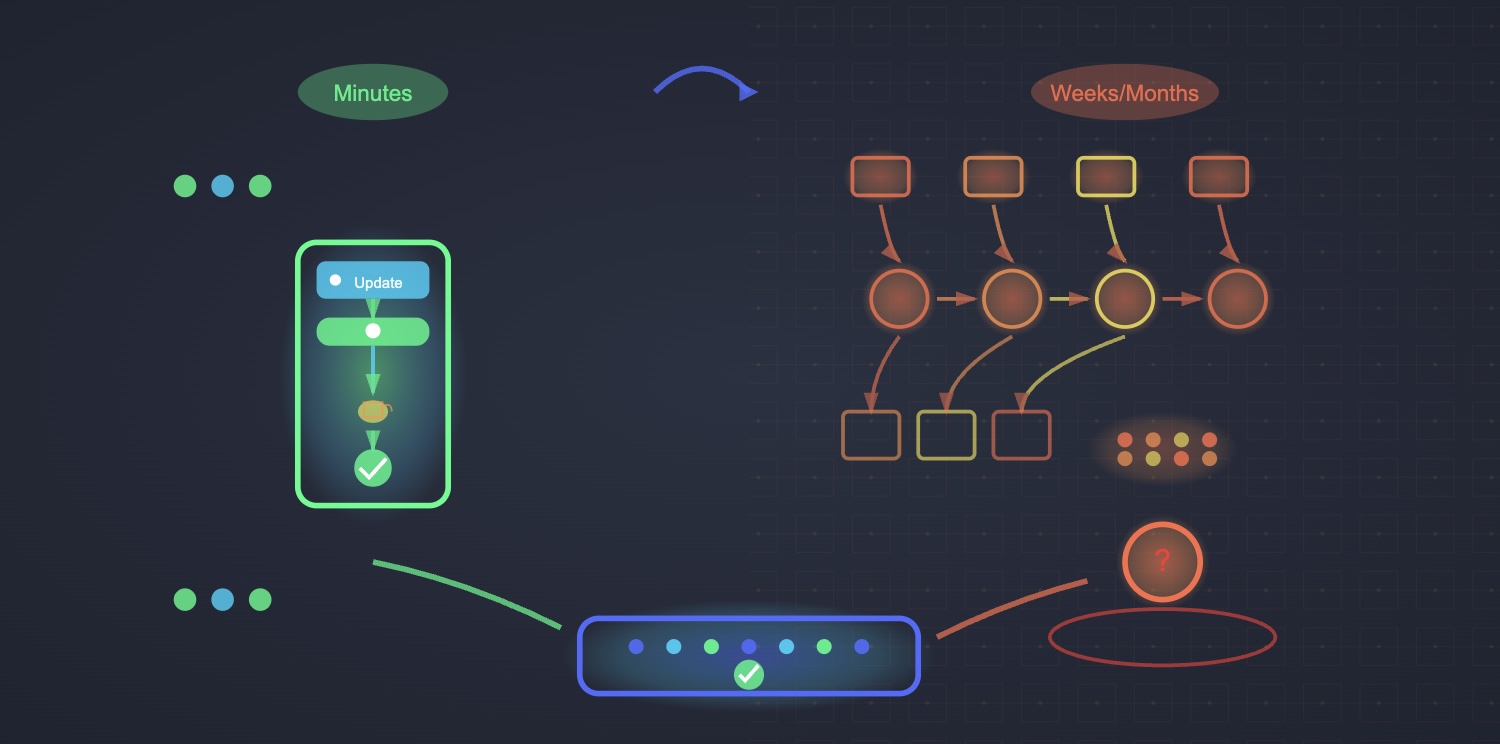
The Never-Ending Battle: Routine Patching vs. Operational Stability
The eternal conflict between cybersecurity teams pushing for rapid patching and IT operations prioritizing system stability is intensifying despite data showing less than 2% of patches cause problems.
Read More →
July 11, 2025
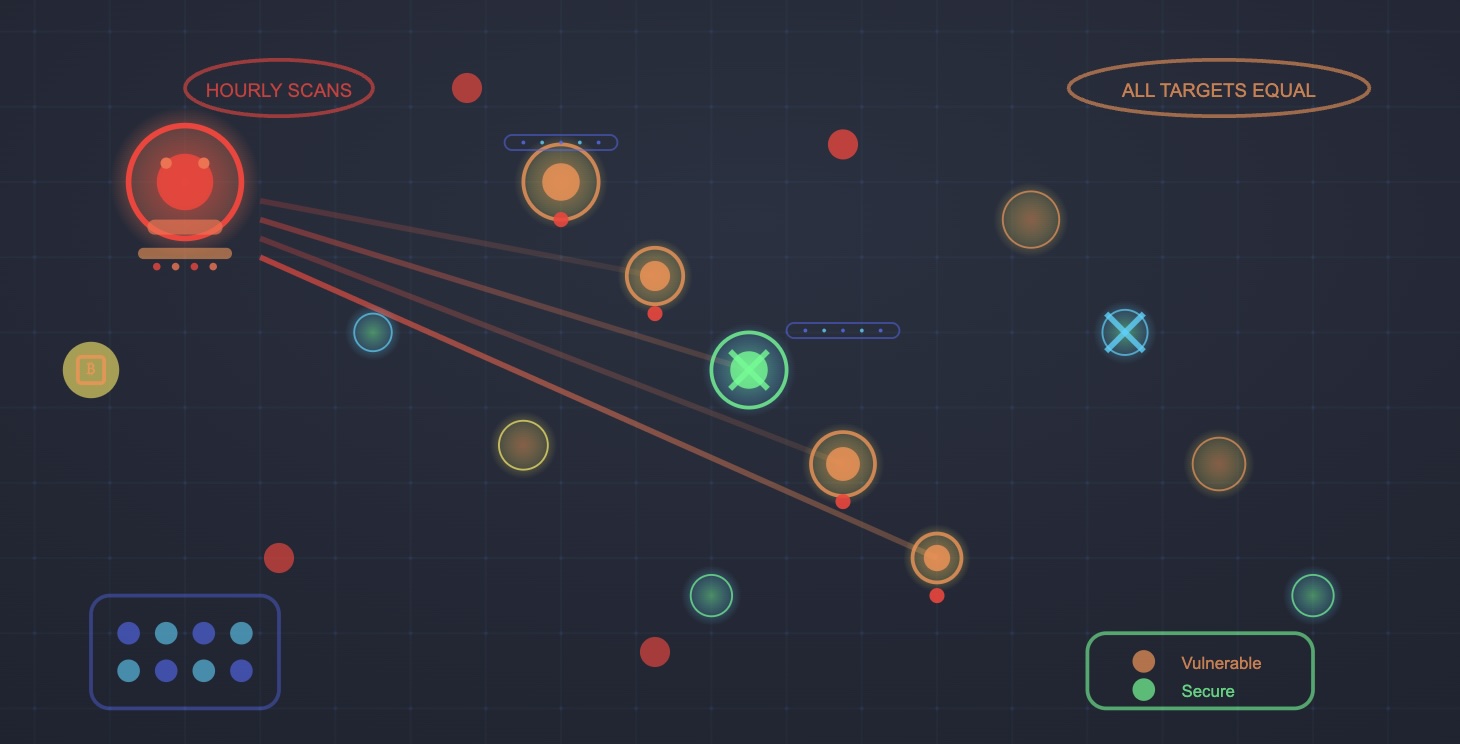
Remember, We're All Just an IP Address to Cyber Criminals
Modern cybercriminals don't target specific organizations—they scan the entire internet for vulnerable systems, making every connected device a potential victim.
Read More →
July 11, 2025
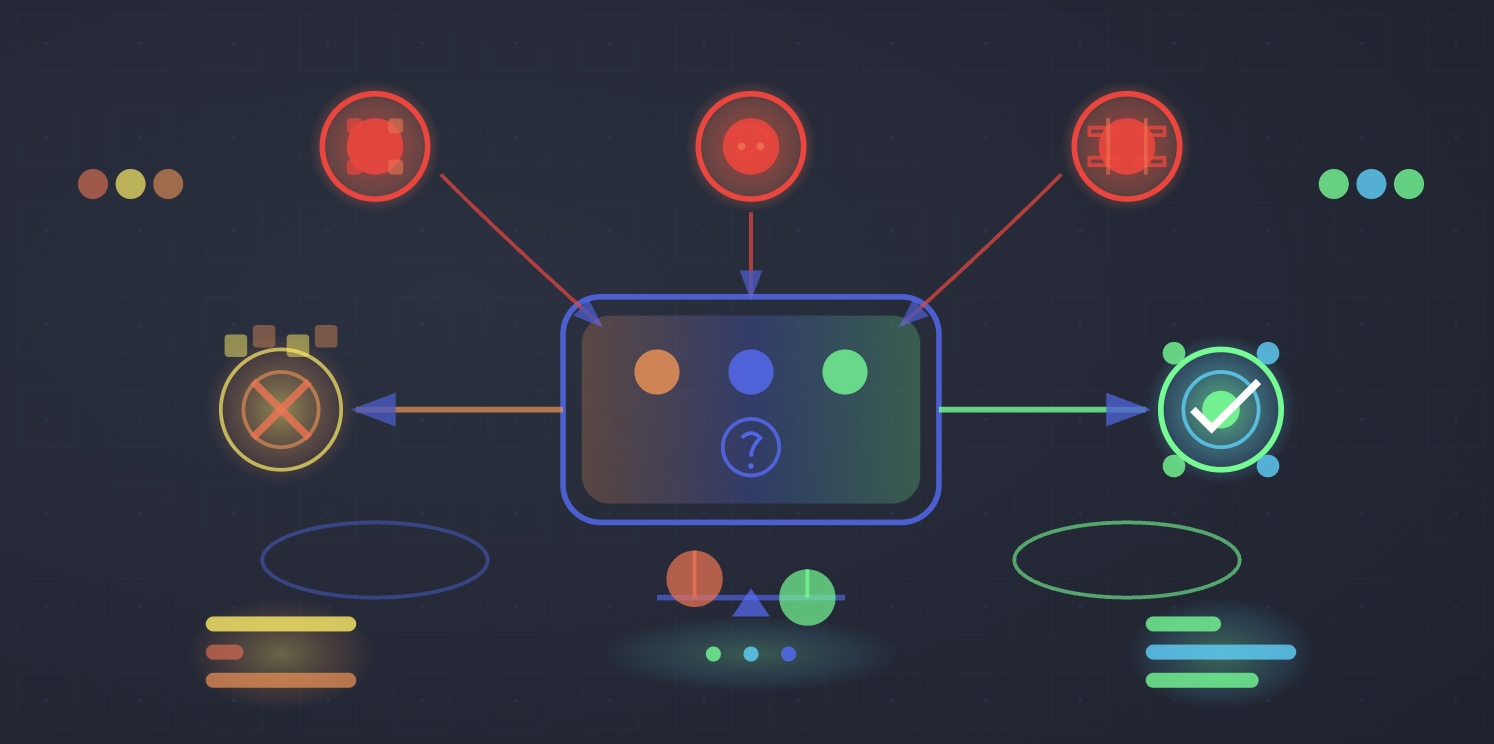
Why Existing Vulnerability Management Solutions Aren't Working
The entire vulnerability management industry has built solutions around everything except the one question that actually matters: "Will this patch break my systems?"
Read More →
July 11, 2025
Weighing Cyber Risk Options: How to Make Objective Cybersecurity Decisions
Effective cybersecurity requires balancing protection with operational efficiency—focusing on the three primary attack vectors while avoiding security theater that burdens teams.
Read More →

July 11, 2025
Providing Cybersecurity to the Underserved, and Building a Business by Doing So
The most innovative cybersecurity companies are discovering that serving underserved organizations isn't just good corporate citizenship—it's a strategic growth approach.
Read More →
July 11, 2025
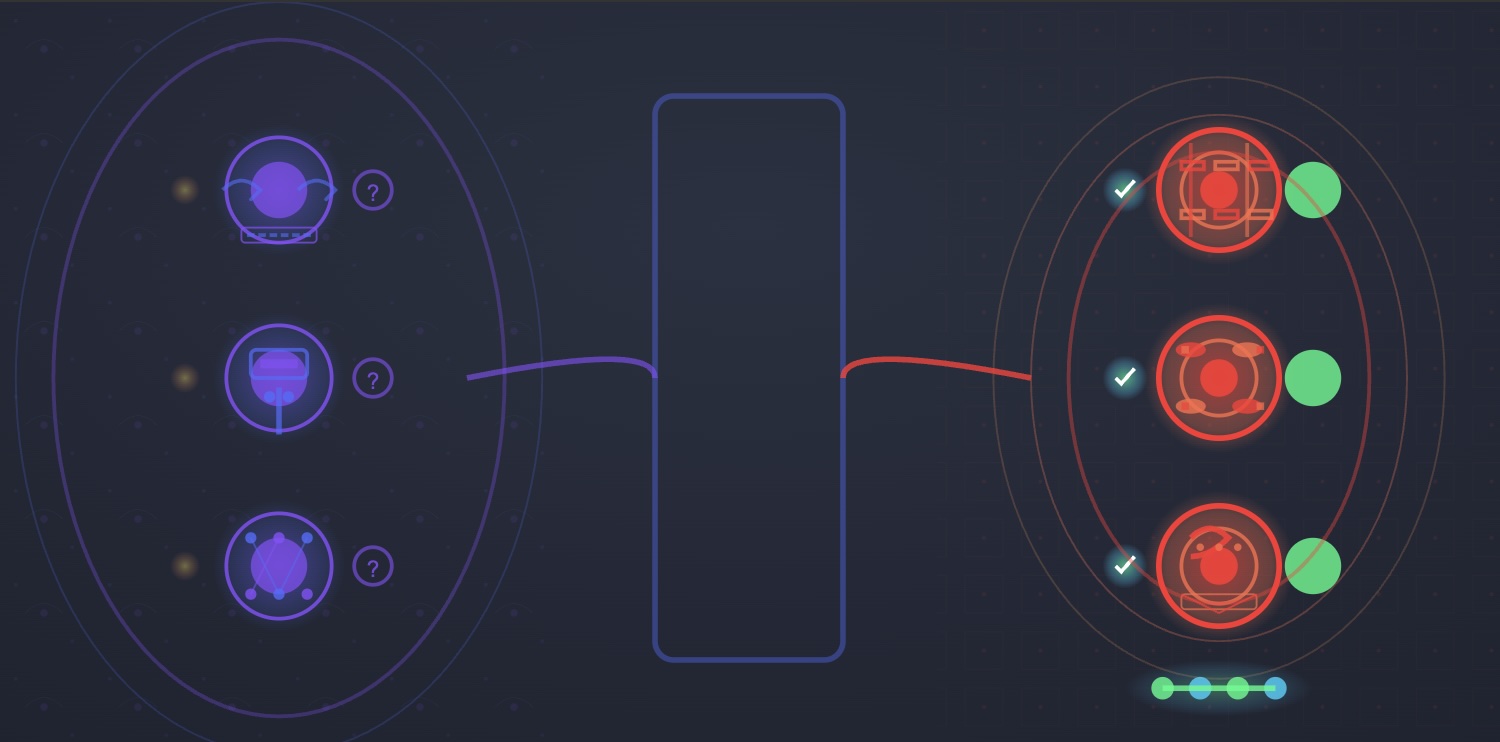
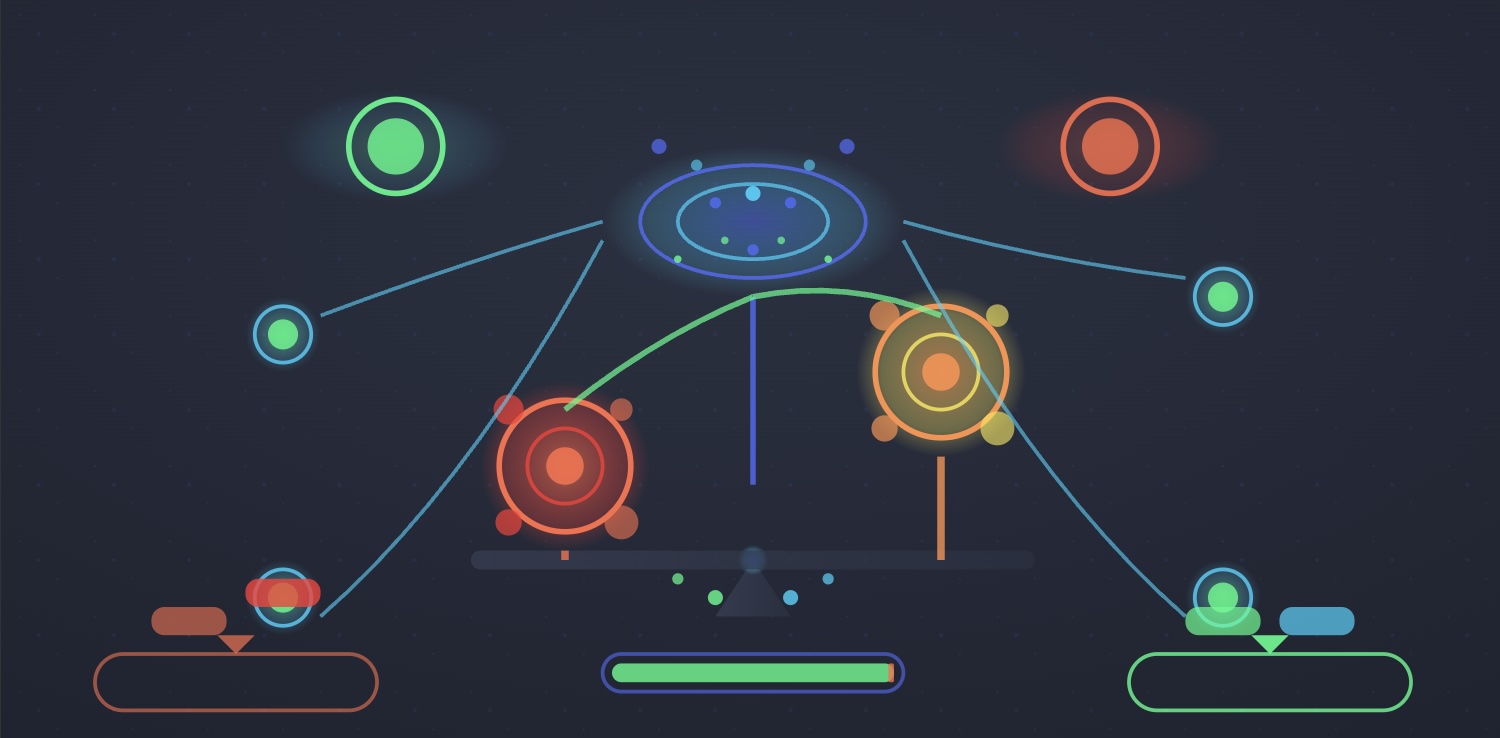
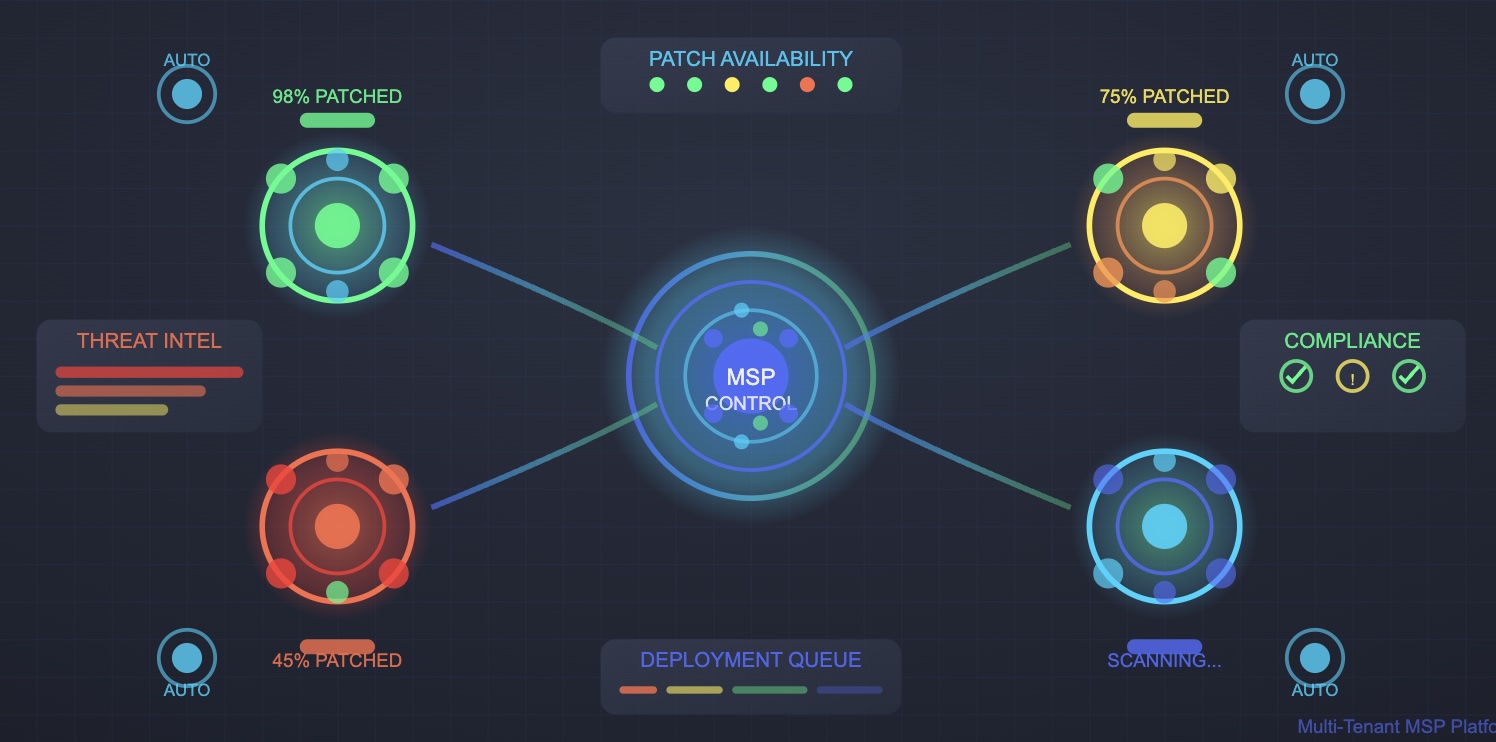
MSP Patch Management: The Delicate Balance Between Operational Risk and Security Risk
MSPs face an impossible choice between patching quickly to prevent breaches and patching cautiously to avoid disruptions—but 98% of patches are safe to deploy immediately.
Read More →
July 11, 2025
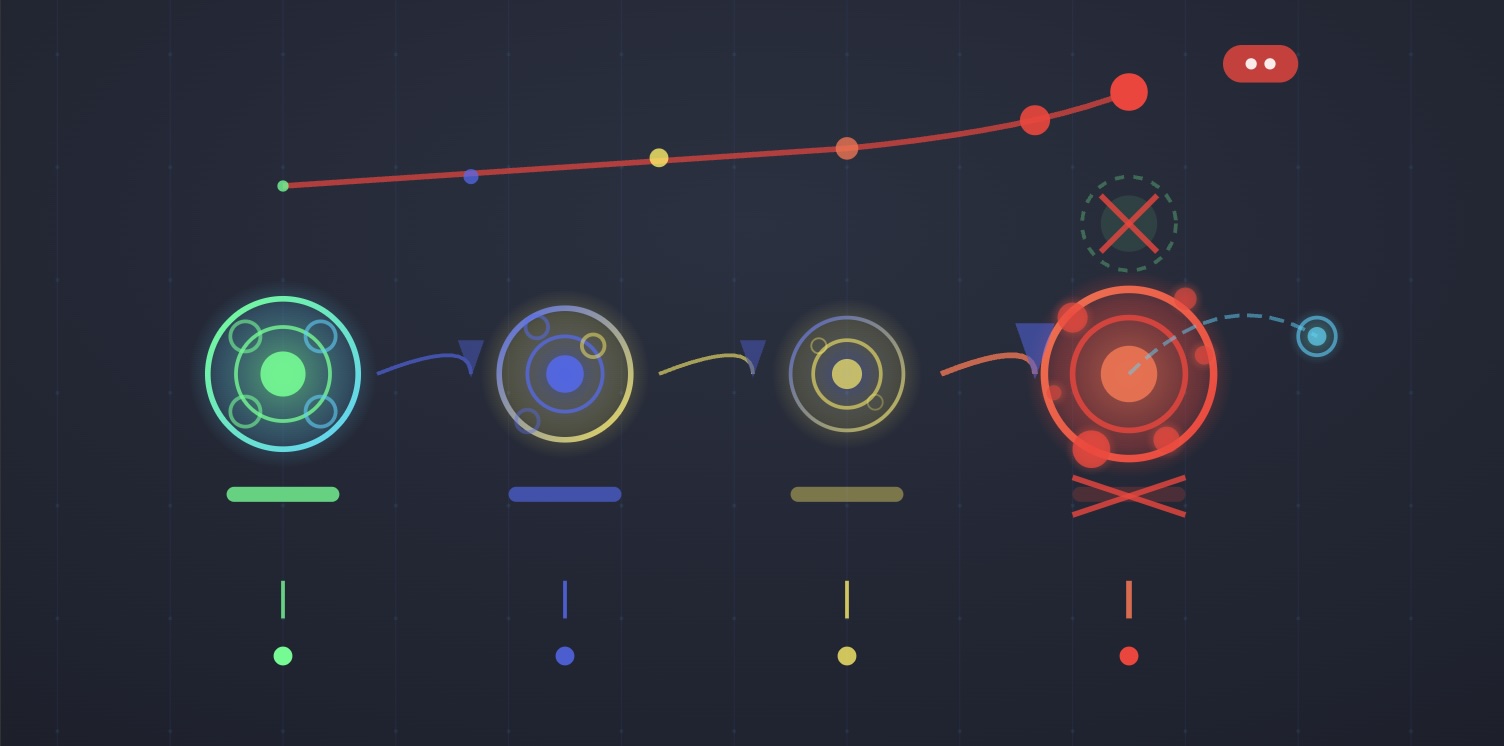
Why Patches Fail: Pending Reboots
Pending reboots cause 17% of all patch failures, creating a cascade effect where security updates stack up and vulnerability windows extend far beyond intended timelines.
Read More →
July 11, 2025
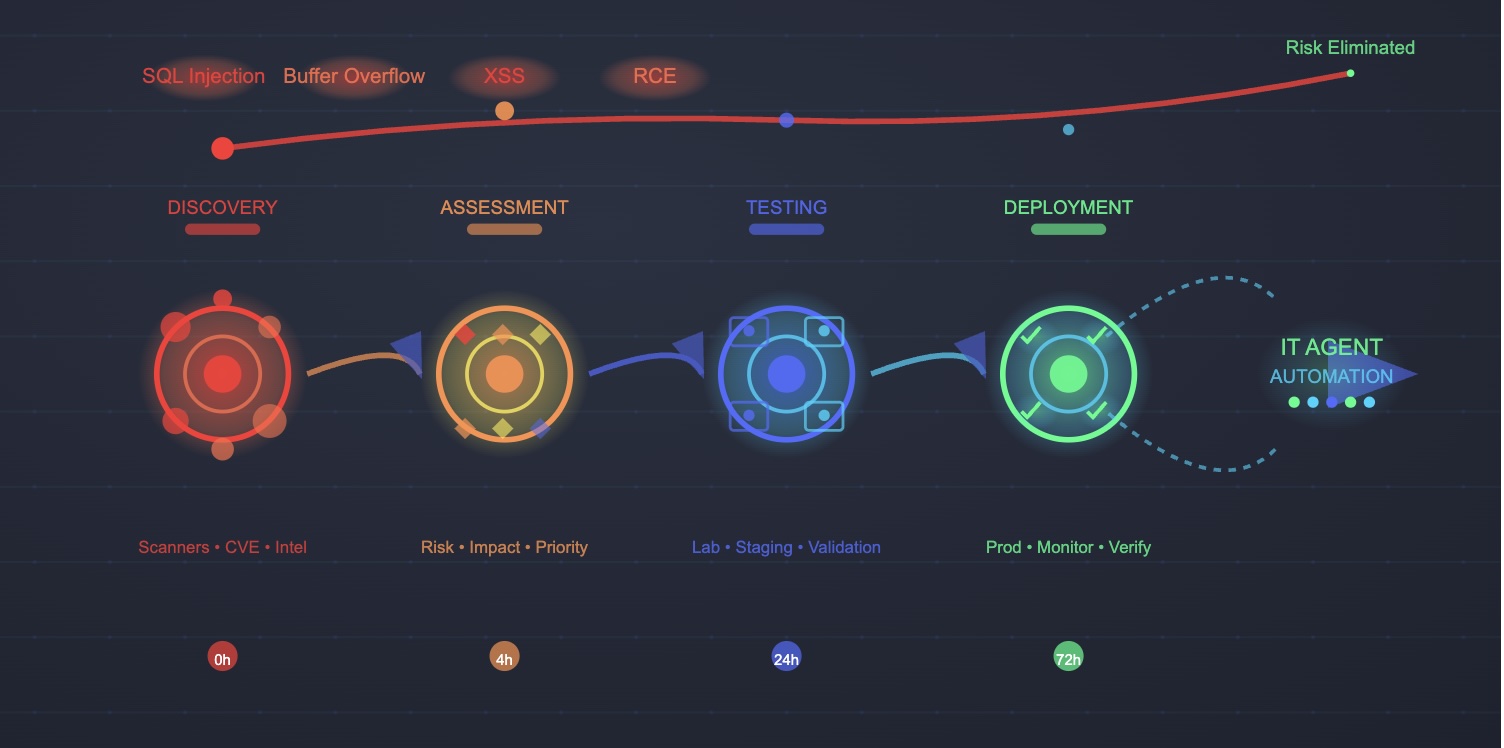
How to Patch Vulnerabilities: A Comprehensive Guide
Effective vulnerability patching requires systematic identification, verification, testing, and deployment processes that balance security urgency with operational stability.
Read More →
July 11, 2025
The Ultimate Guide to Patch Management for MSPs
Effective patch management is the cornerstone of MSP operations, requiring systematic approaches to identification, deployment, and verification that protect client infrastructure.
Read More →
July 11, 2025
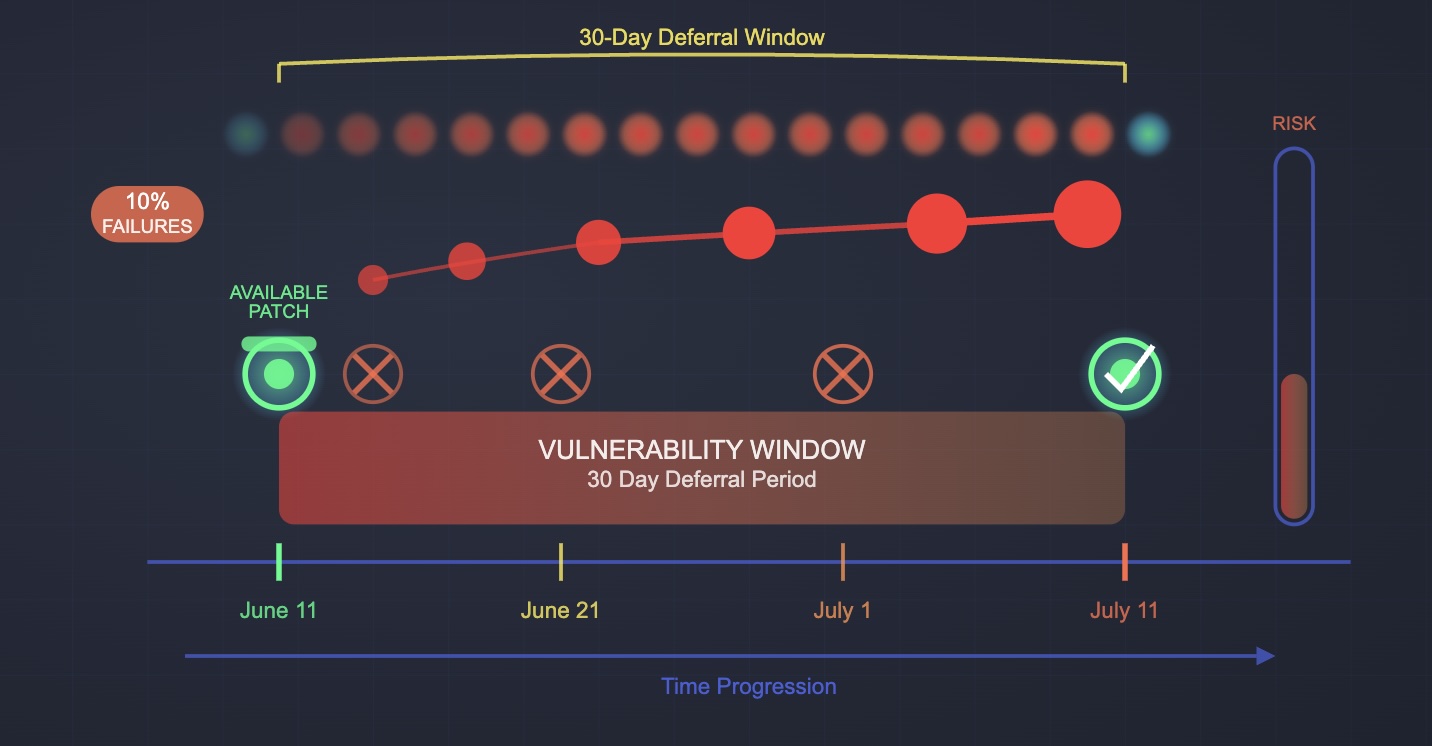
Why Patches Fail: Update Deferral Windows
Deferral windows in endpoint management tools cause up to 10% of patch failures, creating dangerous security gaps while organizations wait for others to test patches.
Read More →
July 11, 2025
Why Patches Fail: End of Life Software
Organizations running end-of-life software are 3.7 times more likely to suffer cyber insurance claims, yet many IT teams unknowingly operate vulnerable EOL systems.
Read More →
July 11, 2025
A Faster Horse
ARPA-H's new healthcare vulnerability program illustrates why the cybersecurity industry remains stuck in outdated practices—building elaborate sandboxes instead of embracing modern patch reliability.
Read More →
July 11, 2025
Why Your Vulnerability Scanner Might Be Lying to You
Vulnerability scanners are supposed to make security teams more effective. Yet many organizations find themselves drowning in false positives, chasing phantom vulnerabilities.
Read More →
%20Caused%20by%20the%20CrowdStrike%20Outage%202024%20IT%20Agent.jpg)
July 11, 2025
The Real Tragedy (Potentially) Caused by the CrowdStrike Outage 2024
The CrowdStrike outage that crashed 8 million Windows devices wasn't caused by a security patch—but the real danger lies in how this incident might discourage critical security updates.
Read More →